One year ago, Russia launched its deadly war against Ukraine. Along with physical violence, attackers tried to break Ukraine down through cyber means. Affecting not only Ukraine but the entire mankind.
"Ukraine is still standing, " said Anastasiia Voitova, a software security engineer with Cossack Labs.
One year of war in Ukraine. A year of death. Homes and cities were destroyed. Let's pray for them and reflect upon the times.

Supply Chain Attack
Today, the rise in security vulnerability is to such an extent that you name it, the world has it. But the one we're going to focus on today is Software Supply Chain. One of the biggest risks in the world of security right now.
Our reliance on third-party and open-source software is exponentially increasing and with time new supply chain issues will unveil their dark sides too. Log4j and Nobelium were just the tips of the iceberg.
Log4j: provided an opening for an attacker to inject malicious code into the logs so it can be executed on the system.
The nation-state attack from NOBELIUM, a Russia-sponsored group of hackers, is widely recognized as the most sophisticated in history. The group gained access to multiple enterprises before their actions were detected.
It won't end:(
The two primary reasons why the supply chain attacks won't stop are -
Our dependence on this third-party software is growing and becoming very attractive for the threat actors to find the soft spots. They could easily convince an insider to manipulate some code in the software supply chain and inject a malicious payload into the software supply chain.
And for certain software, it's almost impossible to resolve to fix those issues because they are pervasive.
And that's what made Log4j such a big thing.
War with Ukraine

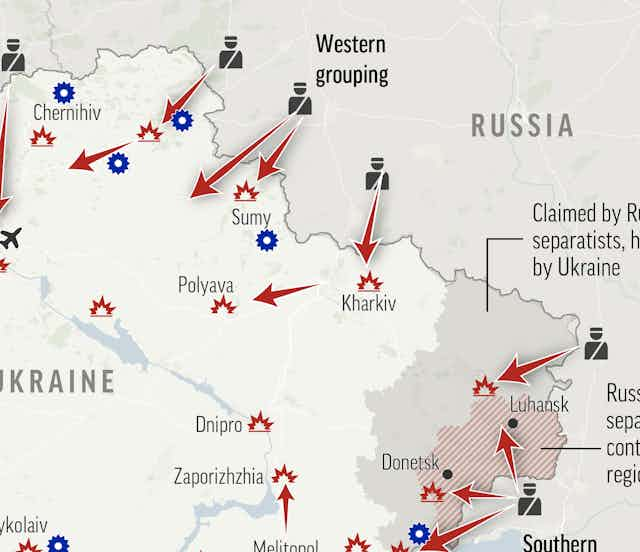
Russia uses a hybrid attack approach. On one hand, there are nation-state threat actors, who conduct these intrusions on the software side. And then there is kinetic military action going on land, air, and sea. Doing all of this in tandem and now it's parallel.
They tried to shut off satellite communications, steal sensitive information, wipe out computer systems crucial to critical infrastructure, and much more. Russia increased its cyberattacks on Ukraine by 250% in 2022 as compared to 2020, according to a report by Google Threat Analysis Group and security company Mandiant.
MICROSOFT: The Messiah
Microsoft worked very closely with Ukraine's cybersecurity agencies and their local enterprises (the private sector) to look at the TTPs, tactics, techniques, and procedures that are used by these threat actors. Then according to this observation, a timeline map was done to see how these threats are unfolding.
The timeline map helped in future predictions of the attacks and shielding from them beforehand. Without this partnership with Microsoft, it wouldn't have been possible to get the end-to-end view that the whole world can see now.
The partnership needs to be continued globally because that's the only way we can defend against these threats.
Addressing the present-day threats
When it comes to addressing the threats - transparency and partnership with collaboration are a necessity. Supporting organizations to be forthcoming with their experience, everybody gets better insights. Supply chain risks are sooner to be found and fixed.
For example, The Nobelium attack, when Microsoft first found out about it, generated a lot of blogs and jargon. And it proved to be very helpful for the larger community because they could use the information and see whether they were getting attacked by the same or not.
CyberSecurity: The Urgency
Speaking of now, there's a perfect storm happening around cybersecurity. Reasons being:
The technology of our devices is getting more and more complex.
Let's think about an analogy, let's say a 1980s automobile and you have your friend who's a mechanic, and he could fix your carburetor for you, that works well in the 1980s. But a 2022 car, you open a hood today and good luck trying to find anything, the technology today is so much more complicated.
The same is true for present-day platforms, whether it be a client platform coupled that we have devices now being used in ways never envisioned before.
Workers that are outside the four walls of the company, the remote workers, and customers all around the world, are subject to different kinds of attacks.
And the combination of the above-mentioned three things continues to evolve, and the nature of these attacks tends to be more and more complicated, and more nuanced along with different devices that are being used with present-day technology. All have conspired to make the environment, a challenging one from a security standpoint.
So how will we survive in these hard times?
Power of Collective
The world is taking a huge lesson from this war i.e., the power of the collective, sticking altogether against attacks, and transparency among each other. Collaboration across the private and the public sector is the way forward in cybersecurity.
In the spirit of collaboration, a trio that's coming upfront in the field of security namely: SBOMs, Sigstore, and Confidential Computing. A powerful joint initiative. They have come forward to establish a joint goal to work towards this whole-of security approach for cyber security.

SigStore + SBOM + Confidential C2
~ They are preparing for the "next Log4Shell", there are some technologies that are emerging on the horizon, among which SBOMs, Sigstore, and Confidential Computing.
Log4shell: A critical security flaw in the Log4j framework is allowing cybercriminals to compromise vulnerable systems with just a single malicious code injection.
~ While SBOMs (Software Bill Of Materials) allow developers to track the dependencies of their software and ensure that they are using secure and reliable packages, Sigstore allows developers to verify the authenticity and integrity of open-source packages, ensuring that the code has not been tampered with or compromised, Confidential Computing, on the other hand, protects code and data in use by performing the computation in a hardware-based, attested Trusted Execution Environment, ensuring that sensitive code and data cannot be accessed or tampered by unauthorized parties, even if an attacker were to gain access to the computing infrastructure.
~ SBOMs, Sigstore, and Confidential Computing provide a powerful combination to address security concerns and ensure the integrity and safety of open-source software and data. They focus on “security first,” rather than perpetuating existing approaches that have typically attempted to bolt on security measures after development, or which rely on multiple semi-connected processes through the development process to provide marginal improvements to the overall security of an application and its deployment.
Check out the speech by OSI's Community Manager Nick Vidal for the 25th celebration of open source.
2023: The Sliver of Hope
What happens now in 2023? It's the hope that war will end.

The surge, innovation, and technology during the war will translate into a big benefit. Not just in Ukraine but in the entire world. The world has its lesson.
Peace.
